Each process is a program or part of a program that is running.
Unfortunately, malware creators know this and are known to hide malicious software behind the names of legitimate processes.
Svchost.exe
The Service Host, or svchost.exe, is a shared-service process.

It allows various other Windows services to share processes.
This helps to reduce resource usage, making the system more efficient.
You will almost certainly see more than one instance of Svchost.exe in Task Manager, but this is normal.
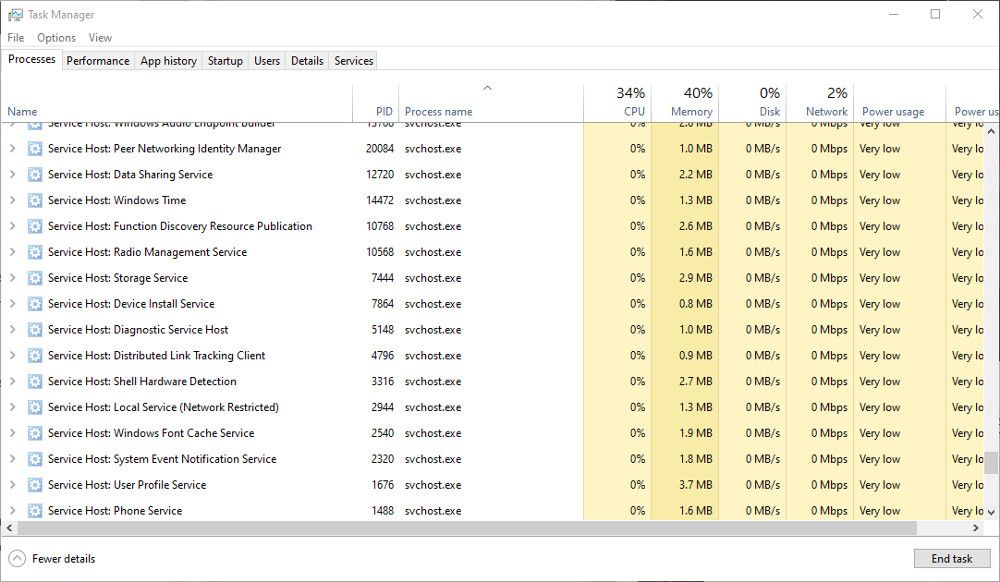
The legitimate Svchost files should be found inC:\Windows\System32.
If you suspect it has been hijacked, checkC:\Windows\Temp.
If you see svchost.exe here, it could be a malicious file.
Scan the file with your antivirus software, and quarantine it if necessary.
Explorer.exe
Explorer.exe is responsible for the graphical shell.
Without it, you would have no Taskbar, Start Menu, File Manager, or even the Desktop.
Therefore, it is an essential part of Windows and cannot be disabled.
Several viruses can use the Explorer.exe filename to hide behind, including trojan.w32.ZAPCHAST.
The legitimate file will be inC:\Windows.
If you find it inSystem32, you should definitely check it with your antivirus software.
Winlogon.exe
The Winlogon.exe process is an essential part of the Windows OS.
It handles things like loading the user profile during login and locking the computer when the screensaver runs.
Unfortunately, because it handles security elements, Windows Logon and the winlogon.exe process are common targets for threats.
Several Trojan viruses, including Vundo, can be hidden within or disguised as winlogon.exe.
The usual location of the Winlogon.exe file isC:\Windows\System32.
If you find it inC:\Windows\WinSecurity, it could be malicious.
One good indication that the process has been hijacked is unusually high memory use.
Viruses and malware don’t just hide behind Windows processes.
Here are someother ways malware can go undetected and hide on your gear.
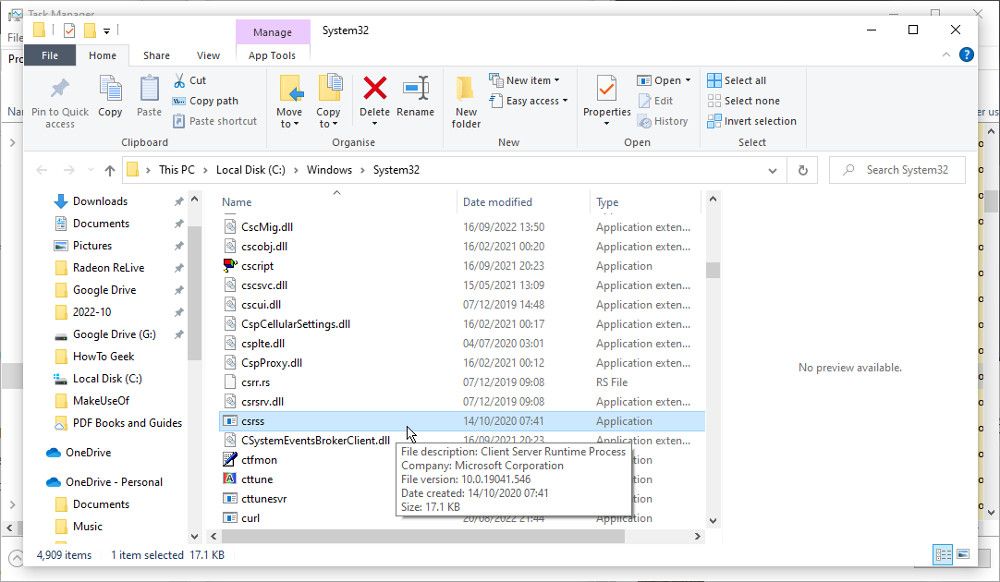
Csrss.exe
The Client/Server Run-Time Subsystem, or Csrss.exe, is an essential Windows process.
The legitimate file should be located in theSystem32orSysWOW64folders.
Right-tap on the Csrss.exe process in Task Manager and chooseOpen File Location.
If it is located anywhere else, it is likely to be a malicious file.
Lsass.exe
lsass.exe is an essential process responsible for the security policy on Windows.
It verifies the login name and password, among other security procedures.
It is unlikely that the process will be hijacked.
If it isn’t running correctly, you will usually be automatically logged out of your box.
But viruses are known to use the filename to hide.
Look for the Lsass.exe file inC:\Windows\System32.
This is the only place you should find it.
Services.exe
The Services.exe process is responsible for starting and stopping various essential Windows services.
If the file is hijacked, you may notice problems during the startup and shutdown of your PC.
Look for the real Services.exe file in theSystem32folder.
If it is located anywhere else, such as inC:\Windows\ConnectionStatus, the file could be a virus.
The processes mentioned here are essential to the smooth running of Windows.
But not all are, and many non-essentialprocesses can even be closed to help with performance.
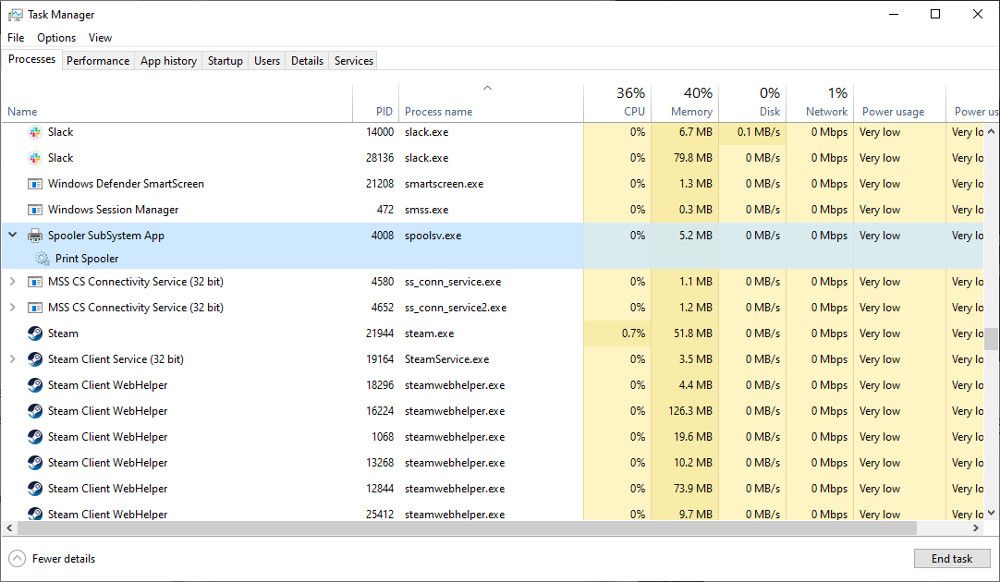
Spoolsv.exe
The Windows Print Spooler Service, or Spoolsv.exe, is an important part of the printing interface.
It runs in the background, waiting to manage things like the print queue when required.
Perhaps because Spoolsv.exe is easily overlooked, a virus can take the name to make itself seem legitimate.
The true spools file can be found inC:\Windows\System32.
The fake file will often appear inC:\Windows, or in a user profile folder.
How Do You verify if a Process Is Legitimate?
The Task Manager is your friend when looking for suspicious activity.
Infected processes will often behave erratically, consuming more CPU power and memory than is usual.
Most of the essential processes listed here should only appear in the System32 folder.
you could easily check the location of a suspicious file in the Task Manager.
Right-opt for process and selectOpen File Location.
Check the path of the folder that opens to ensure the file is in the correct place.
Another way to tell if a file is legitimate is to check the size.
Most of the .exe files of these essential processes will be under 200kb.
Right-press the process name in Task Manager, selectPropertiesand look at the size.
If it seems unusually large, take a closer look to determine if it is safe.
you’re free to alsocheck the certificate of the EXE file.
An authentic file will have a security certificate issued by Microsoft.
If you see anything else, it is likely to be malicious.
The final thing to do is scan suspect files with an up-to-date antivirus scanner.
Quarantine and remove any files that are flagged as infected.
Sometimes a malicious file will behave oddly, using too much CPU and memory.
So spotting a suspicious file in other ways is a useful skill.